The
next-generation VPN
As easy as making a video call: XplicitTrust simplifies network access, making VPNs and network security less of a hassle.
Start your 30-day free trial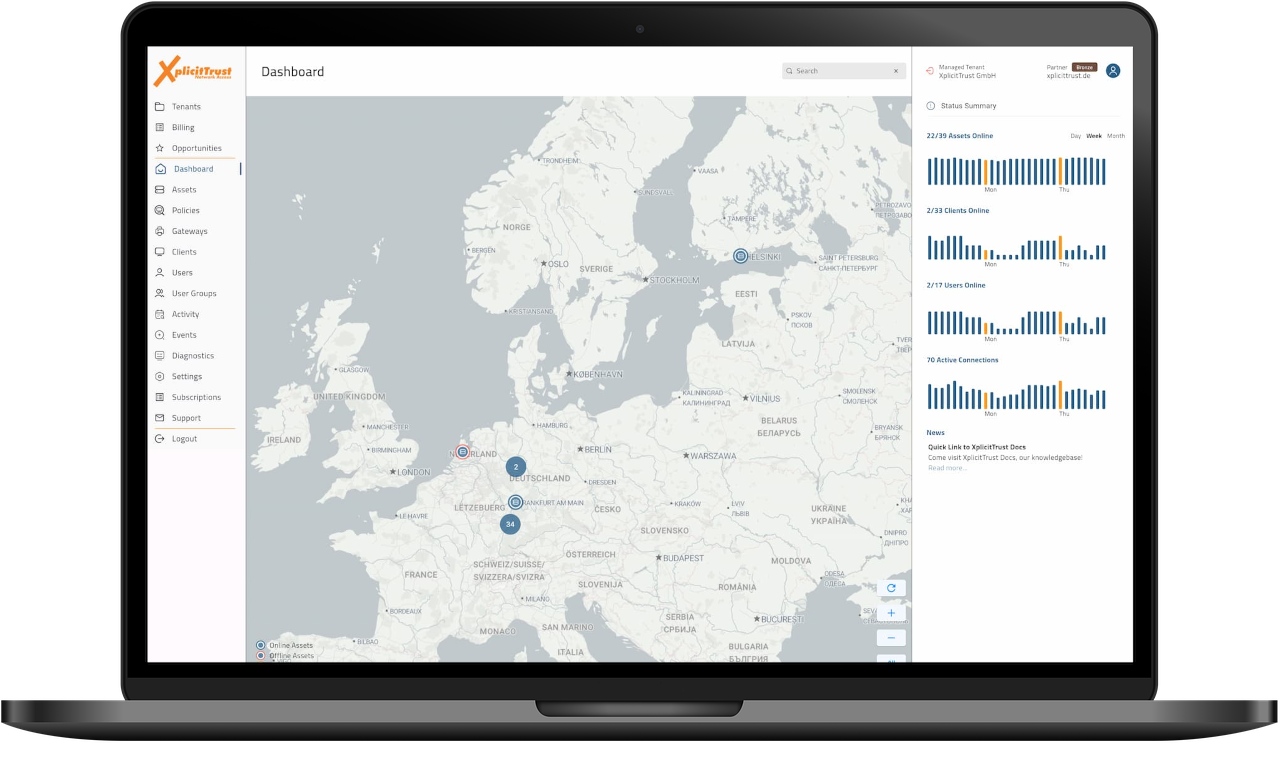
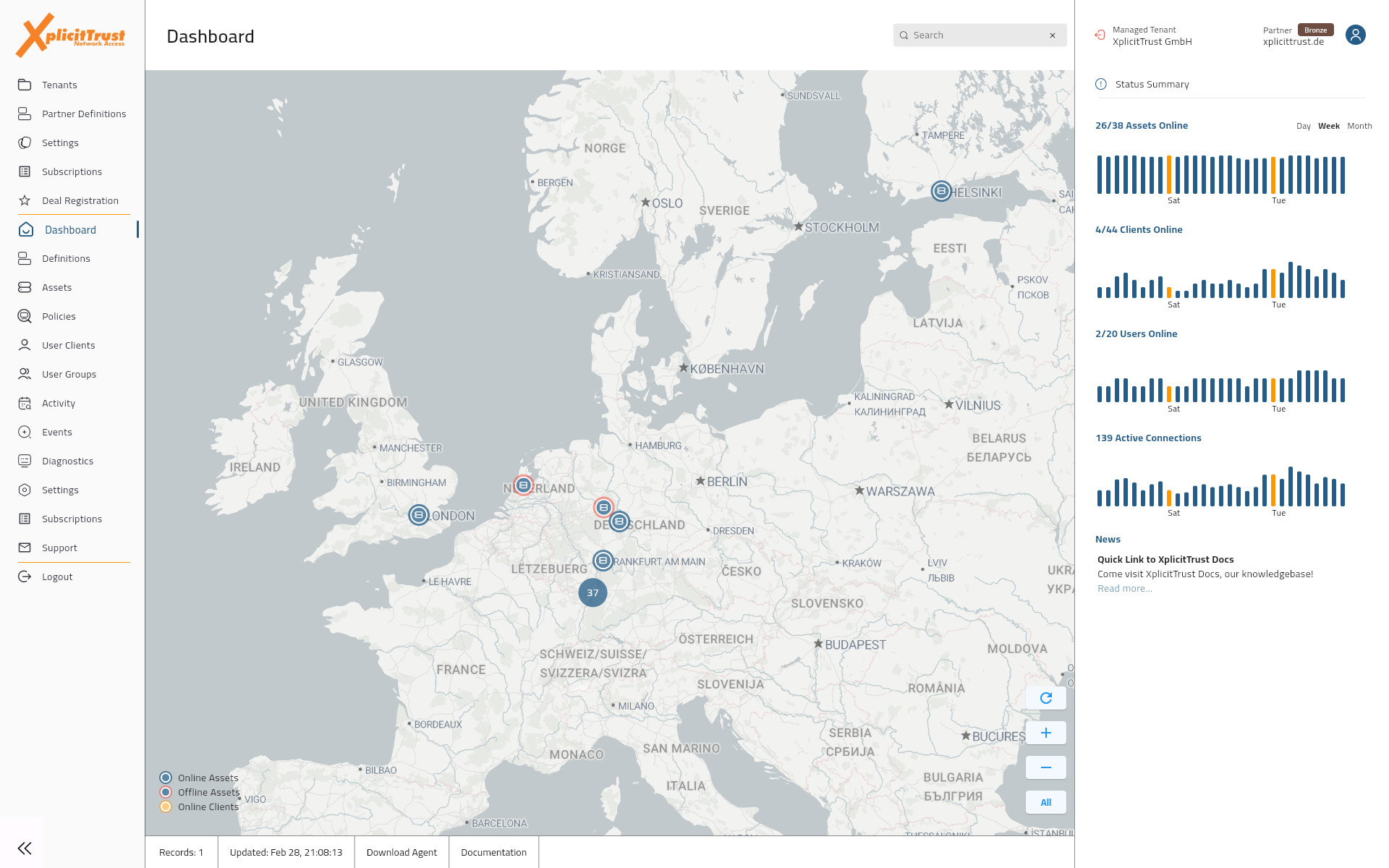
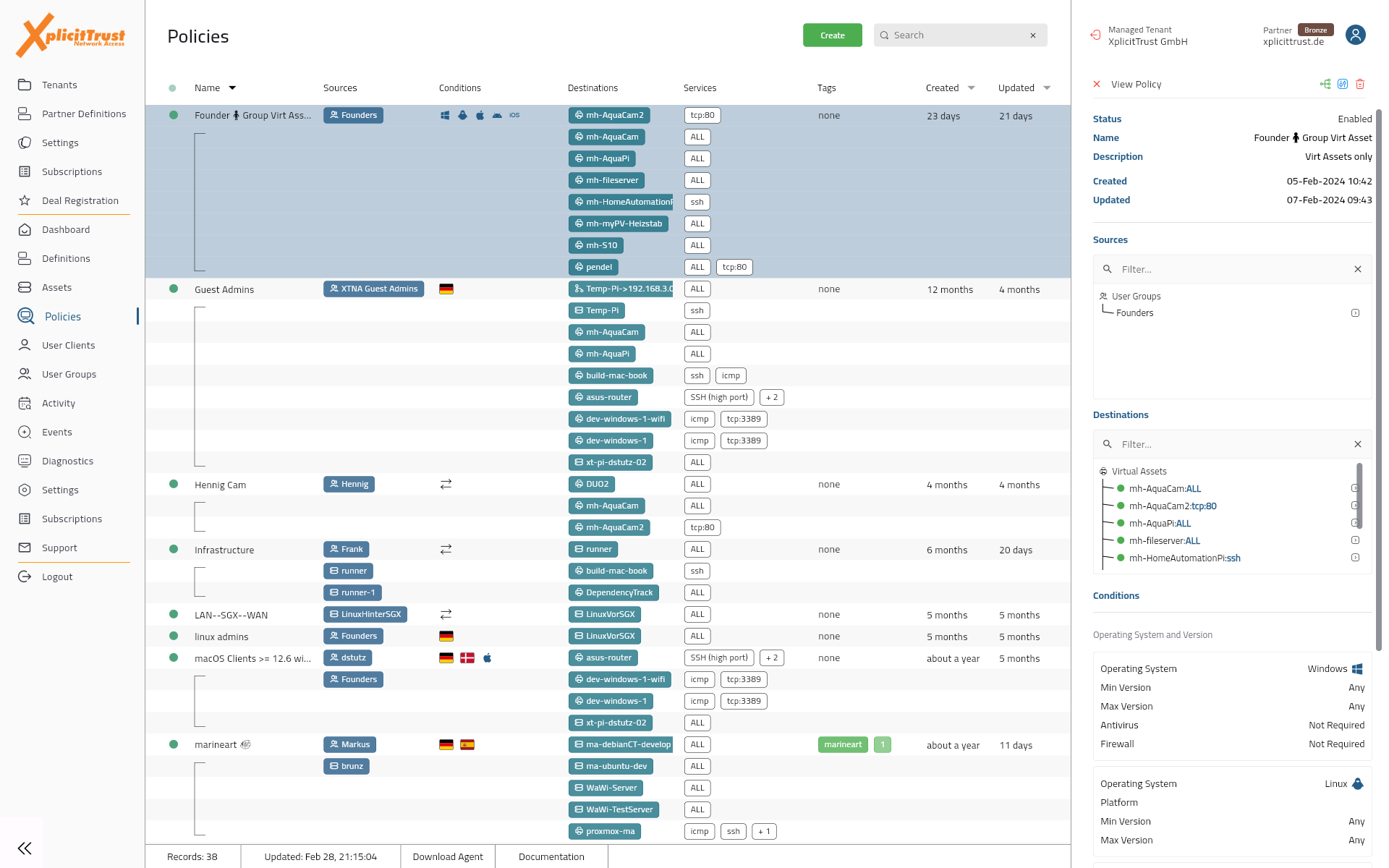
What admins reach for every day
Access control, live topology, diagnostics, and a clean asset inventory in one console.
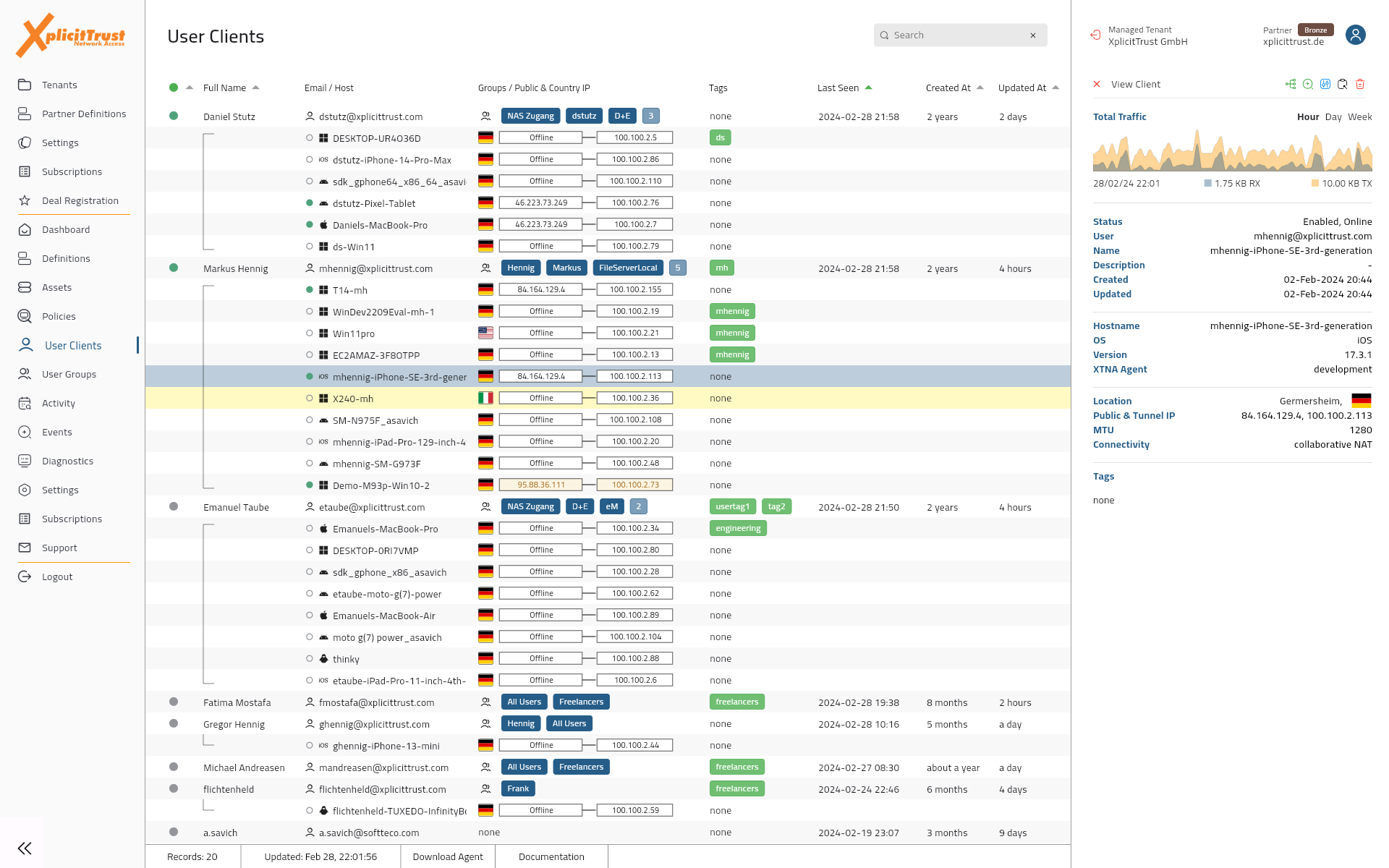
Decide who reaches what, by identity
Authenticate users against the IdP you already trust and gate access by group, device posture, location, or time. No flat networks, no broad VLAN trust.
- SSO with MFA via Microsoft Entra, Google, Keycloak, BareID
- Conditional rules across posture, location, and time
- See at a glance which devices a policy permits
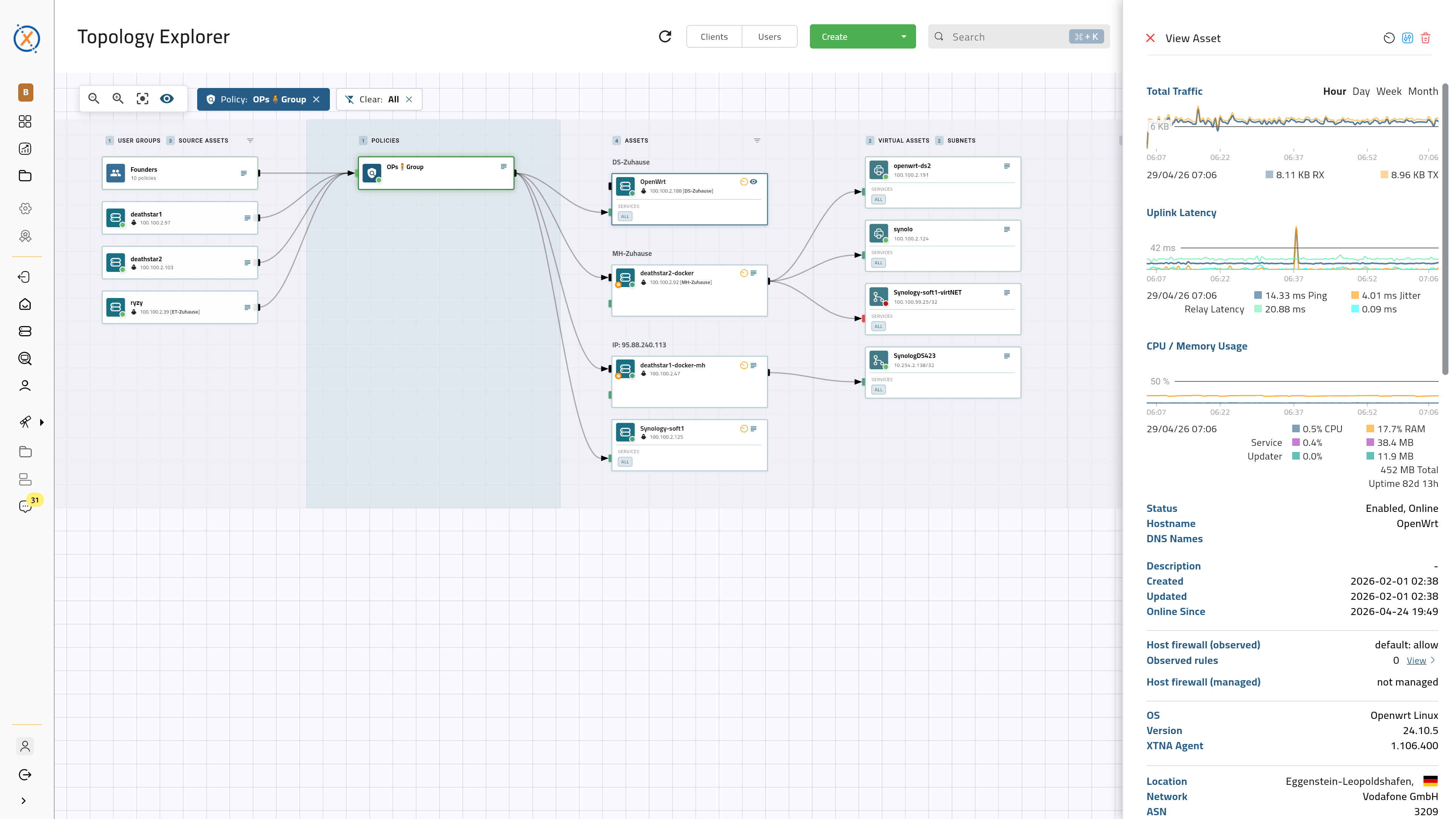
A mental model for the whole network
User groups, policies, and assets as one graph admins can read at a glance and edit in place. Pairs with Learning Mode and Network Discovery so rollouts start with the network you already have.
- Inspect and reconfigure policies and assets directly in the graph
- Picks up Learning Mode traffic and discovered hosts for easy rollouts
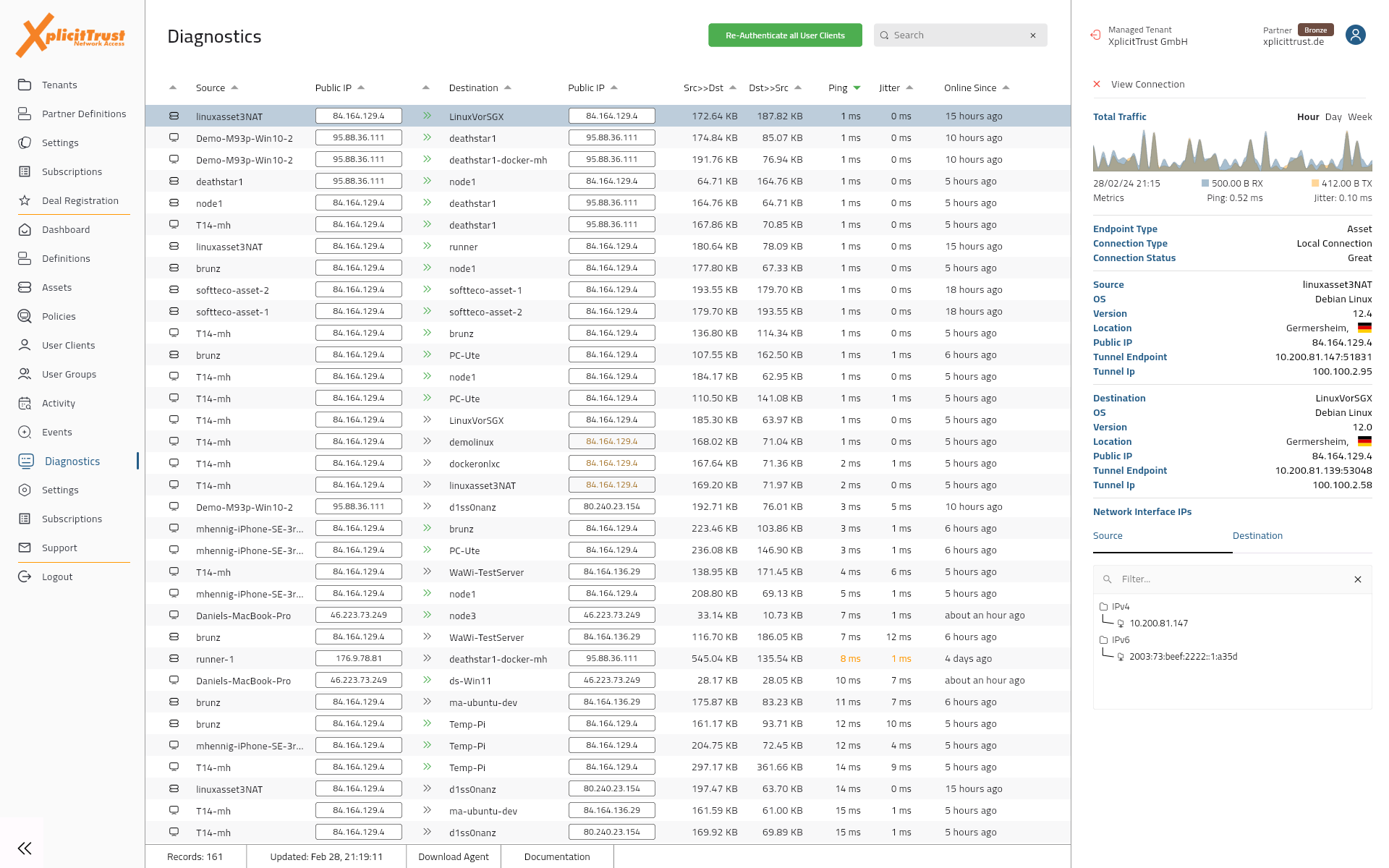
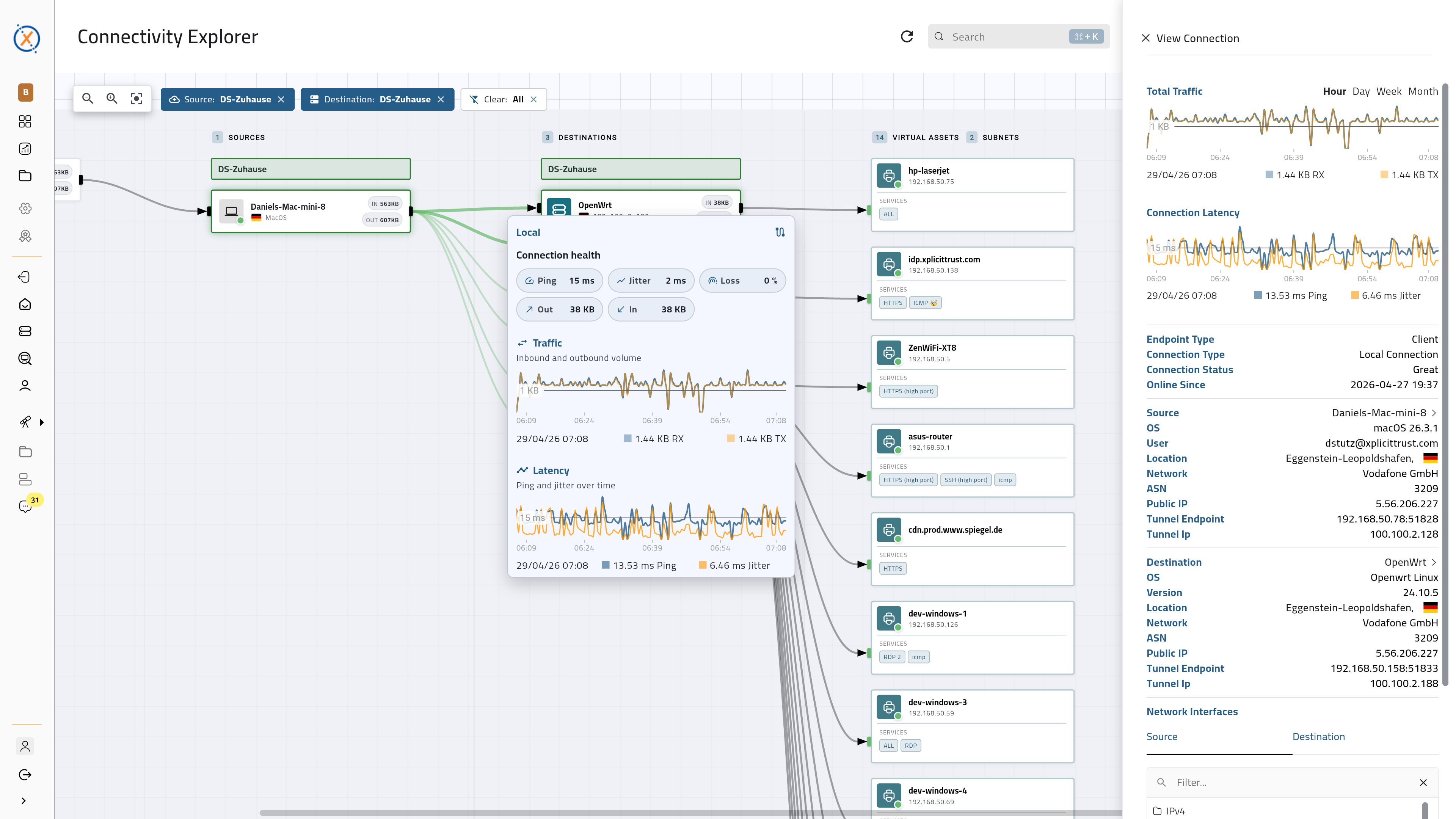
Live tunnel telemetry next to host load
Per-connection RTT, jitter, packet loss, and traffic, alongside CPU and memory usage on each end. Query by user, location, or application server to find where a slowdown actually lives.
- RTT, jitter, packet loss, and traffic per tunnel, in real time
- Cross-reference connection metrics with host CPU and RAM
- Query by user, location, or application server
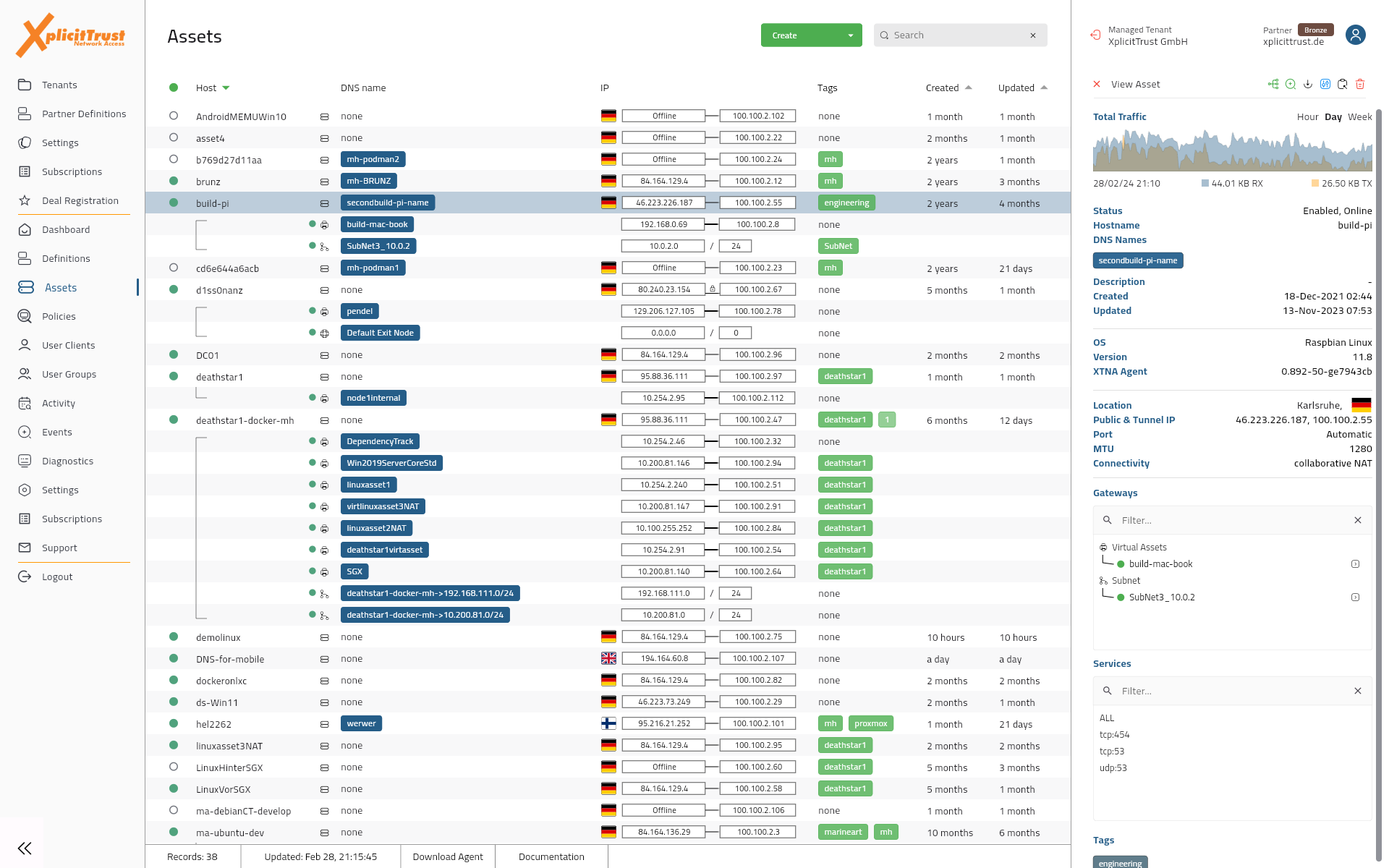
Every server, printer, and camera in one list
Catalog every network asset that delivers something to your business and see exactly which policies grant access. No tabs full of spreadsheets, no per-site audit drift.
- One inventory for servers, IoT, containers, and cloud services
- Virtual resources for systems that can't run an agent
- Optional egress routing through inspection or enforcement points
Modern Network Access
XplicitTrust simplifies network access, making VPNs and network security less of a hassle. It's as easy as making a video call.
Simple Installation
Clients are lightweight, install in a heartbeat, and simply ask for the user's email address, nothing else.
Zero-Configuration Clients
No client configuration necessary. After single sign-on, clients automatically receive their configuration and keys.
Single-Sign On & MFA
Single sign-on and multi-factor authentication. User changes from your identity provider are reflected instantly.
Static IP Addresses
Each device gets a fixed IP address on the overlay network, to avoid collisions with your existing IP addresses.
No Need to Touch Firewalls
We operate independently of your firewalls. No need to make firewall or network configuration changes.
Connect from Anywhere
Works from anywhere. Inside your networks, on the road, from home, in cloud data centers, and more.
Seamless Roaming
No connection loss when you move between locations, WLAN access points, internet providers, and uplinks.
Firewall & NAT Traversal
We automatically traverse firewalls and complex NAT. All while keeping your traffic end-to-end encrypted.
Internal Domain Names
Reach any device using a friendly internal domain name of your choice. Or simply use its IP address.
Zero Trust Policy Engine
Every connection is evaluated continuously against identity, device posture, and access policies. The XplicitTrust Zero Trust Policy Engine decides who reaches which application, from where, and on what terms.

Highly Secure
Our platform is built around state-of-the art encryption, access control, and security best practices.
Powerful Encryption
We rely on a powerful combination of modern, peer-reviewed cryptographic algorithms.
End-to-End Protection
End-to-end encryption. Private keys exist on your machines only. We cannot see what's inside your packets.
Automatic Key Rotation
Keys are automatically rotated on all devices every few minutes, for perfect forward secrecy.
Single Packet Authorization
Devices will only respond to authenticated packets, anything else will simply be dropped.
Zero Trust Network Access
Continuous evaluation of location, time, device and security info to check access context according to configured policies.
Precise Access Controls
Precisely control what each user and machine can access, via our policy engine. Enforced at destination.